What are OTA updates in Application Management Edge?
Keeping software, firmware, and applications up to date across a large set of distributed sites and devices is becoming one of the central challenges in modern deployment models. As more intelligence moves out of the datacenter and into vehicles, equipment, and remote locations, the need for reliable and secure over-the-air processes grows quickly.
Historically, OTA largely meant replacing the entire software image on a device, without the ability to update individual applications or components. As a result, upgrades were infrequent and often postponed, because each update carried operational risk and typically required a full system restart.
Edge Device OTA refers to delivering fine-grained updates directly to devices operating in the field, often with limited connectivity and without physical access. This capability is increasingly important as organizations depend on distributed edge environments that must stay secure, compliant, and functional without manual intervention.What is an OTA Update?
What is an OTA Update?
An over-the-air update is a remote software, firmware, or application update that occurs without physical access to the device. OTA makes it possible to patch security issues and deploy new functionality across distributed environments. Historically, OTA replaced the full system image, but modern approaches separate operating systems and applications to enable smaller and more frequent changes.
Categories of OTA Updates include
- Image updates: complete image for the device
- Operating system updates: updates of the underlying operating system
- Application updates: updating individual applications, multiple applications exist at the edge with their own lifecycle
- Configuration and policy updates: modern applications separate configuration and policies from the code. This means flexible different configurations at different locations.
Modern edge environments increasingly depend on application-level OTA to avoid full-image replacements and to deliver updates continuously.
Why OTA Updates Matter in Edge & Application Management
Edge sites often run standard Linux distributions together with individual containerized applications such as MQTT brokers, edge AI models, local HMIs, or small databases. Each of these components evolves at its own pace and needs to be updated independently, rather than forcing a full image replacement across every site.
Modern regulations and internal security practices (including CRA) require frequent patching of both operating systems and applications. At the same time, operational requirements differ between edge locations, making it necessary to adjust configuration, certificates, and policies per site.
OTA, therefore, becomes a key mechanism for keeping distributed edge environments secure and up to date, while enabling continuous improvements without manual intervention or physical access.
Key Benefits & Value of OTA Updates for Application Management
Remote deployment allows teams to deliver changes to software and configuration without visiting sites, which is essential when devices run in industrial or geographically distributed environments. Secure rollout strategies, such as canary releases and automated rollback, reduce the risk of downtime and support continuous improvement.
OTA also enables feature variation, where different edge sites can run different applications or versions depending on local needs. This avoids the “one image fits all” constraint and supports more flexible operational models.
By reducing manual work and allowing faster, incremental updates, OTA scales application management across large fleets and helps organizations keep pace with security, compliance, and functional requirements.
How OTA Updates Work in Edge/Application Environments
With the illustration below, we will now outline how OTA updates operate in edge environments and how the different components interact during deployment.
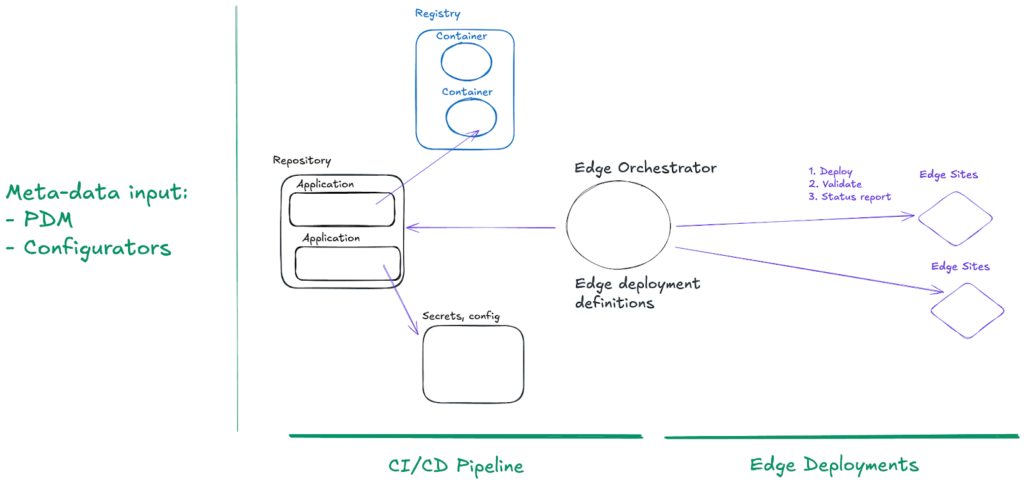
An OTA process for edge applications is typically driven by an edge orchestrator capable of handling tens of thousands of distributed sites with intermittent connectivity. The orchestrator manages deployment specifications and ensures that each site receives the correct set of components before anything is started.
Application artifacts reside in standard repositories and refer to container images in container registries. Alongside each application are associated configurations and secrets, for example, unique certificates per edge site. These must be part of the deployment process and handled automatically rather than manually injected.
Different edge locations often require different applications or versions depending on the environment and equipment. Deployment specifications, therefore, define which applications should reach which sites. Each edge site is autonomously responsible for starting and validating the application start, and reporting status back to the orchestrator. At runtime, rollout strategies such as canary, rolling, and rollback are essential for safe updates at scale.
Upstream, metadata sources like PDM systems and product configurators typically feed into CI/CD pipelines, which in turn drive application artifacts and deployment logic for the edge.
Challenges & Risks of OTA Updates at the Edge
Edge environments often operate with intermittent connectivity, which makes reliable delivery and verification of updates more difficult than in datacenter environments. Distributed sites also run heterogeneous hardware and software versions, so update logic must adapt to local capabilities rather than assuming a uniform platform.
Security and integrity of updates become critical when devices are remotely updated. Each artifact, configuration, and secret needs to be validated, and rollback mechanisms must be in place if something fails. Monitoring application start-up, health, and post-deployment behavior across many sites adds further complexity.
Historically, full firmware replacement guaranteed that all components worked together as a tested image, whereas modern fine-grained updates introduce the risk that a single component or dependency breaks intended functionality if not handled carefully.
How Avassa Supports OTA Updates and Edge Application Management
The Avassa Edge Platform contains two software components:

- The Avassa Control Tower provides central orchestration of distributed edge resources and containerized applications through user interfaces and APIs. It is available as a service or can be installed on private infrastructure. It embeds a distributed secrets manager.
- The Avassa Edge Enforcer is a software agent installed on all hosts in all edge sites. It provides zero-touch host registration functions, local site management, application placement and scheduling, and a local container registry. In addition, the Avassa Edge Enforcer provides local APIs for secrets management and distributed event streaming for applications that require such services.
The Avassa Edge Platform is designed for distributed edge environments where connectivity is unreliable, and applications evolve independently. The platform downloads only the minimal changes required, can restart transfers when connectivity is lost, and uses caching and replication between hosts at a site to reduce bandwidth.
In long-lived disconnected scenarios, the Avassa Edge Platform continues to drive each site toward the desired state without manual retries. Multi-architecture container support and device discovery ensure that the correct applications start on the hosts that actually have the associated hardware, for example, a camera mount or sensor interface. On top of connectivity challenges, edge OTA also needs to happen at scale – the Avassa Edge Platform regularly proves scalability.
Secrets are delivered through a built-in distributed secrets manager, where each secret is validated, and images are checked for consistency before applications start. The edge enforcer monitors startup and health at the site and reports results to the orchestrator, enabling safe actions such as stopping or rolling back if needed.
Each application is managed separately with its own versioning, health checks, and update cycle, which isolates failures and allows targeted remediation without disturbing other applications running at the edge
Conclusion
As edge environments grow in scale and complexity, OTA updates become essential for keeping distributed systems secure, functional, and continuously improving. The shift from full-image replacements to fine-grained application updates reflects how modern edge and IoT deployments operate: modular, containerized, and constantly evolving. OTA updates will continue to be a critical part of modern edge computing and IoT operations in the future, particularly as more intelligence moves away from centralized datacenters and into devices and applications running at the edge.
