Avassa Edge Platform: Scalable Edge Application Management
Deploy. Scale. Secure. The Next-Gen Edge Computing Solution.
Avassa Edge Platform is a leading edge computing platform designed for seamless edge deployment, application lifecycle management, and container orchestration. Whether you’re managing a single application across hundreds or thousands of locations, or a diverse set of workloads across a varying set of infrastructure, Avassa provides a secure, scalable, and efficient edge platform solution.

Seamless Edge Deployment, Management, and Orchestration
Your distributed containerized applications need lifecycle management, monitoring, security, multi-tenancy, and OS upgrades.
What if you had an easy-to-use tool for managing all your containerized applications, VMs, and operating system upgrades at the edge, extending the tooling you’ve come to love from central cloud environments?
Avassa’s application-centric edge platform helps you manage and monitor edge systems and containerized edge applications. With applications deployed in many locations, you need extra care and control. Avassa provides automated and efficient placement and versioning functionality of containers as well as the ability to monitor and observe application health with ease. You can also perform operating system updates as well as utilize support for VMs for your not-yet-containerized workloads.
Container Application Management & Operations
Define applications using standard container practices.
Remote Site Monitoring & Onboarding
A comprehensive inventory of all edge locations and their available resources.
Scalable Edge Deployments: From Cloud to Edge
Combine the two, using targeted edge deployments, and only place and monitor applications where it makes sense.
DID YOU KNOW
By 2028, 80% of custom software running at the physical edge will be deployed in containers?
Gartner, 2023
in cloud
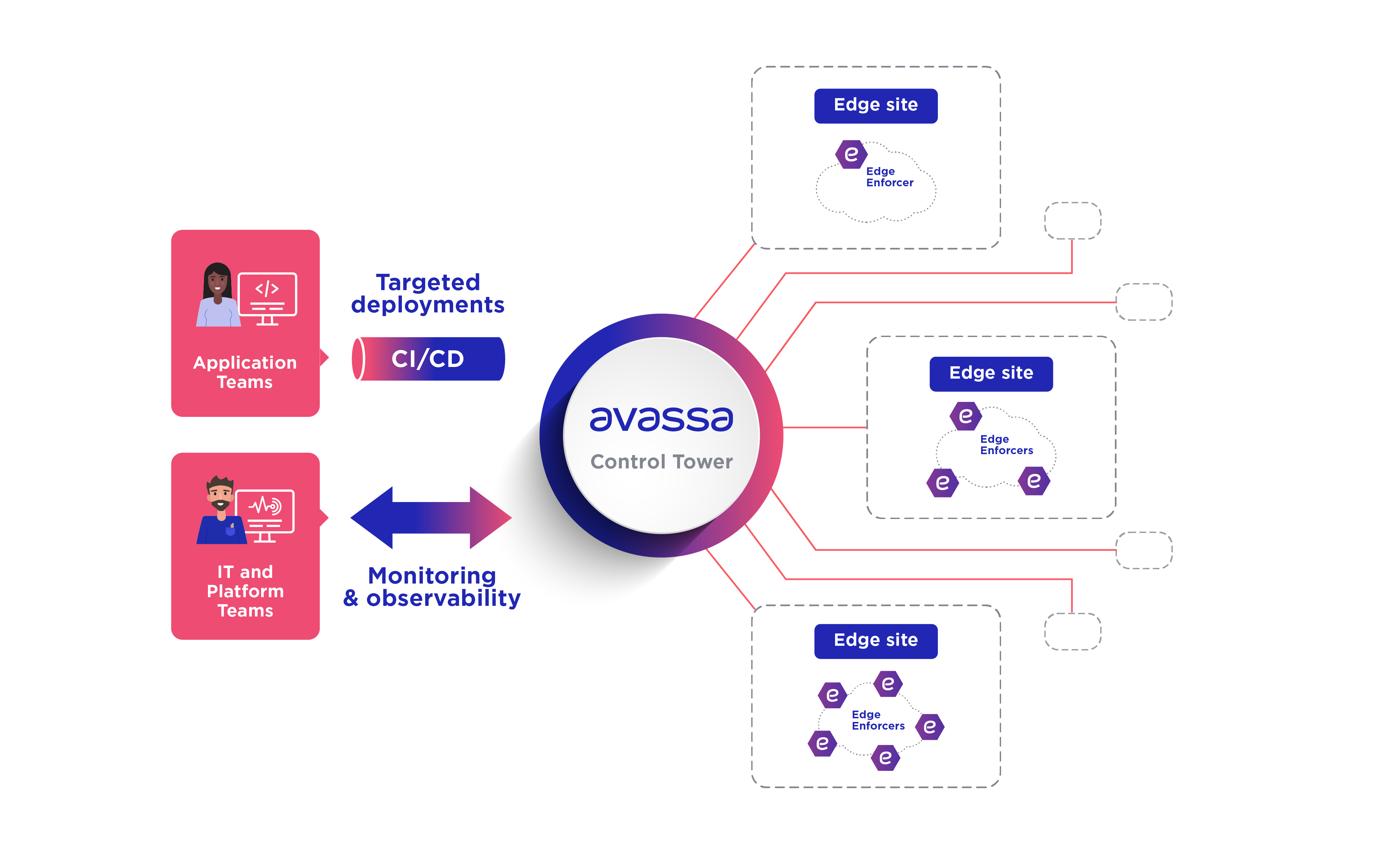
Control Tower: Centralized and Automated Edge Management
The Avassa Control Tower, available as a service or installed on your private data center, does what it says: it controls your distributed containerized applications including VMs, and operating systems updates through user interfaces and APIs.
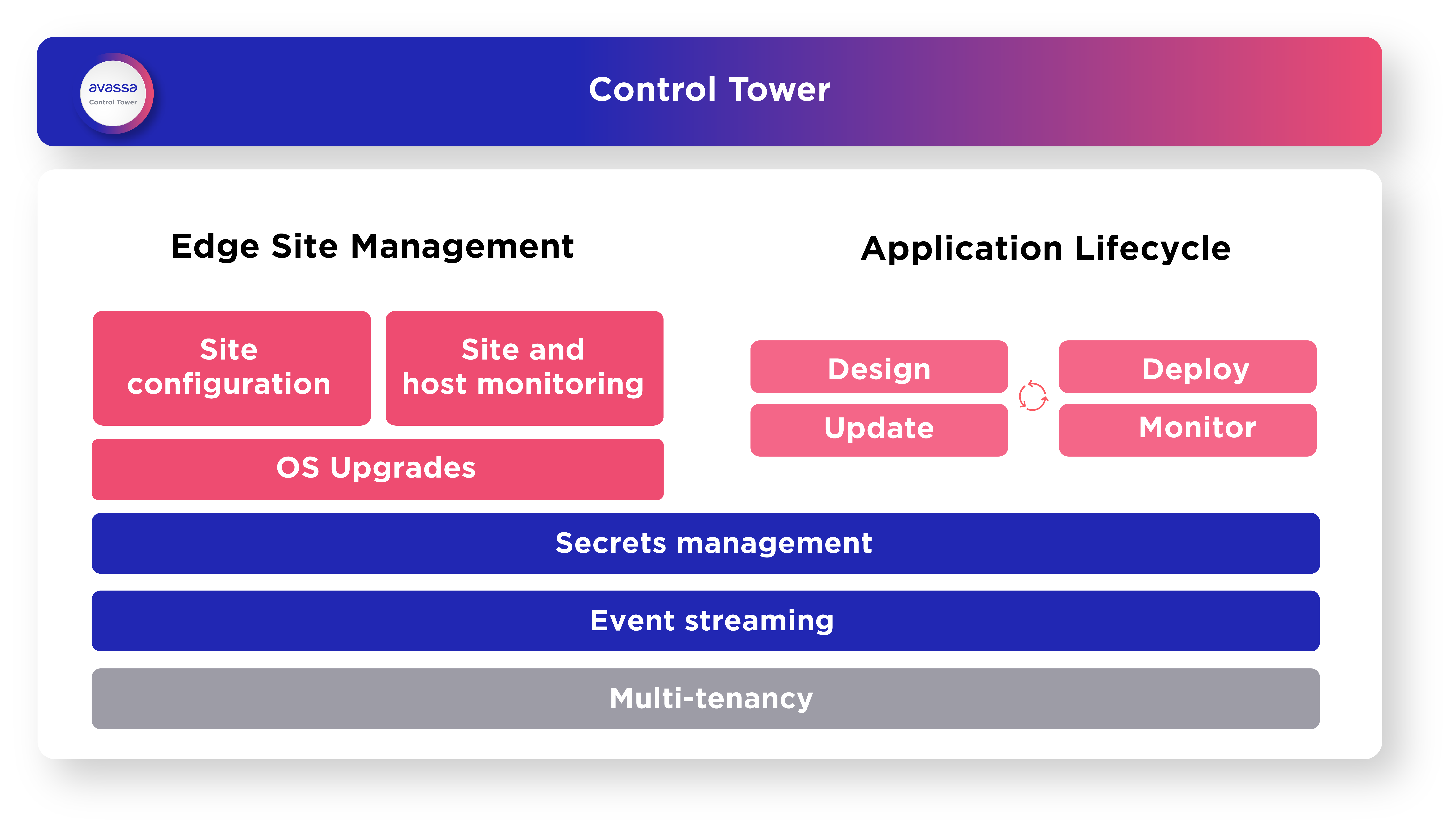
Edge Site Management
Teams in charge of managing distributed compute resources use the Control Tower to:
- Assemble sets of distributed hosts into sites to allow for granular resource assignments for application deployment purposes.
- Proactively monitor your edge applications, as well as the edge hosts and the dependencies in between.
- Perform administrative tasks on the distributed clusters including observing resource consumption for planning purposes or planned maintenance activities without impacting application availability.
- Roll out new versions of the operating system on your edge hosts.
Application Lifecycle
Teams in charge of managing edge applications use the Control Tower to:
- Define applications in terms of constituent containerized applications and VMs, associated application configuration, edge network configuration, and resource needs.
- • Declaratively define deployments across your edge based on label matching. Labels can either be administratively set up or refer to the hosts’ automatically discovered available resources.
- Deploy, upgrade, and change the containerized applications across distributed clusters, including VMs for legacy application workloads.
- End-to-end automation radically reduces the manual work needed to manage applications at scale.
- Monitor the health and observe the behavior of containerized applications.
Common requirements for edge applications are distributed event streaming and secrets management. The Control Tower manages a central repository of secrets that can be selectively distributed to sites and applications with strong security. Each edge site has a local event bus which can be efficiently queried from the Control Tower.
on-site
Edge Enforcer: Secure and Autonomous Edge Sites
The Avassa Edge Enforcer is a container application installed on each host. It provides all required application services to enable unique edge site autonomy and application continuity while having a uniquely small performance footprint.
Avassa Edge Enforcer is a key differentiator compared to many other over-the-top or fleet management solutions. It removes the burden of managing a complex software stack on the edge sites. The Control Tower performs automatic upgrades of the Edge Enforcer.
Edge Enforcer provides secure edge orchestration, containerized application scheduling, and enterprise-grade orchestration for distributed environments.
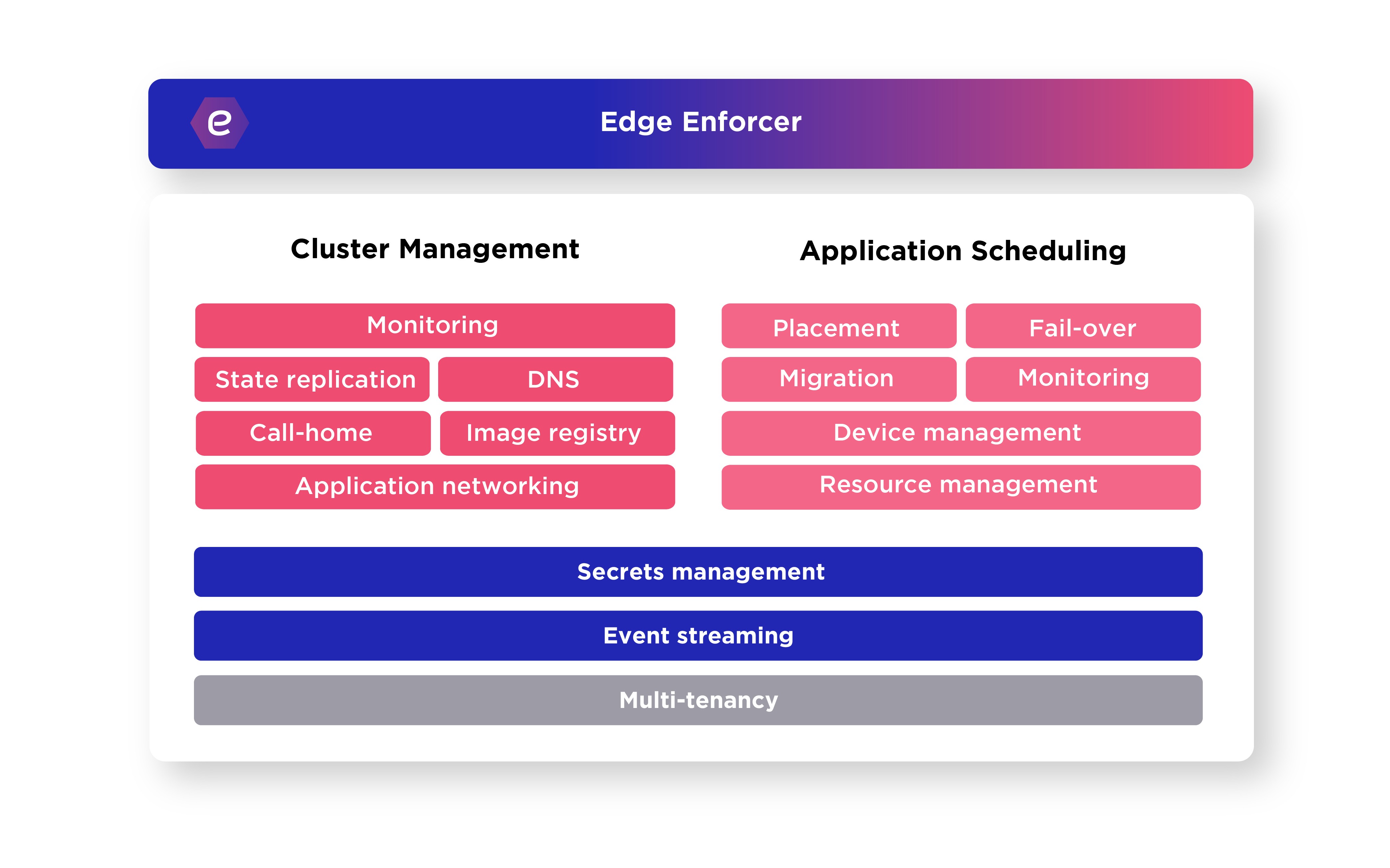
Cluster Management
The Edge Enforcer provides automatic call-home, site-local cluster formation including state replication and a local container registry so that applications can be rescheduled across hosts. It also configures all required application networking including an embedded DNS service. The Edge Enforcer also proactively monitors the operational status of the edge hosts including resource availability. It embeds an OS controller that autonomously manages the OS upgrades on the site as defined by central policies.
Application Scheduling
The Edge Enforcer enables autonomous edge applications, both containers and VMs. On request from the Control Tower, it automatically schedules applications on to edge hosts in the site. Automatic fail-over and migration is built-in as well as local edge host monitoring. The Edge Enforcer discovers local devices such as GPUs or attached cameras so they can be made available to applications. Local host resources are managed to allocate available resources across applications and tenants.
The Edge Enforcer provides cluster-local event streaming and secrets management. Secrets and events are autonomously maintained on the site. The events can be distributed to your central solution. Secrets, in contrast, are configured centrally and securely distributed to the sites.
Avassa in Action – Real-World Success Stories
Learn how leading enterprises use Avassa to streamline edge deployments, container orchestration, and remote management across industries like retail, industrial, and telecom.
Customer Testimonials
Frequently Asked Questions
Data sheet
Operating applications at the distributed edge
Here you can access and download our data sheet for the Avassa Platform to get this information to-go.
demo
Book a demo
Welcome to book a demo of our edge platform. Book a demo at a time slot that is good for you. You’ll receive a calendar invite to the email address that you provide. That’s it! We look forward to showing you around our application orchestration solution for the distributed edge.

DIVE INTO THE DETAILS
Looking for our platform documentation?
Deep-dive into the details of how our solution works in our platform documentation.

Reach out
Interested in learning more about our technology?
Send us a message and we’ll let you know how we can help.






